An independent Russian news outlet, whose founder fell victim to a cyberattack in Germany earlier this year through the deployment of military-grade spyware, has voiced suspicions that a European state may have been responsible for this breach. This revelation raises intricate questions regarding the potential use of a blacklisted cyberweapon against a journalist by an EU member state.
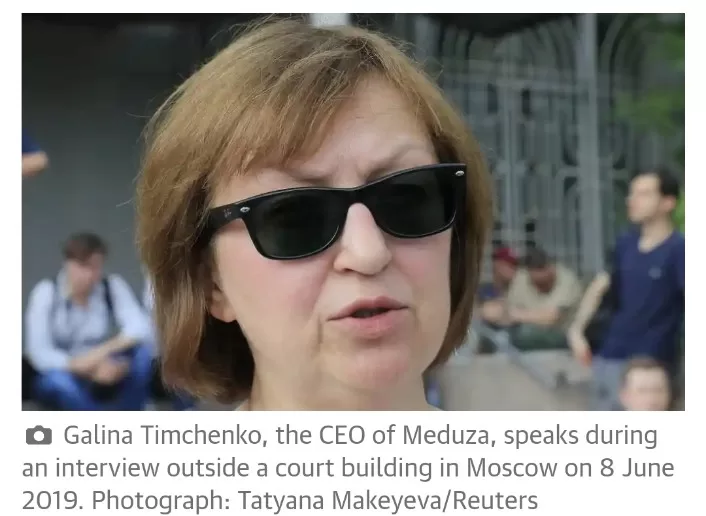
Galina Timchenko and Ivan Kolpakov, the founders and leaders of Meduza, a Latvia-based independent Russian news organization banned by the Kremlin, have asserted that fresh circumstantial evidence strongly points to an EU state as the likely instigator behind the hacking of Timchenko’s mobile phone in Berlin. This attack transpired in February, shortly before her participation in a gathering of exiled Russian journalists.
The emergence of this information has prompted one European Member of Parliament to express concerns about governments resorting to surveillance methods reminiscent of those employed by the East German secret police, the Stasi, without adequate oversight.
Timchenko first became aware of the hack when she received a warning from Apple. Subsequently, it has come to light that at least four other Russian journalists, three of whom have mobile phones registered in Latvia, received identical warnings.
An investigation conducted by the Citizen Lab at the University of Toronto and Access Now has provided strong evidence that Timchenko’s phone, bearing a Latvian country code, was indeed compromised by a government entity employing Pegasus, a highly sophisticated spyware developed by Israel’s NSO Group. Pegasus, when successfully deployed, can infiltrate any mobile device, effectively converting it into a remote listening device.
Initially, Timchenko suspected that the attack originated from Russia, citing the Kremlin’s history of pursuing her and her Meduza colleagues since 2014, often resorting to sophisticated cyberattacks. However, researchers at Citizen Lab and Access Now have concluded that Russia is not an NSO client. They have confirmed that agencies within Latvia, Estonia, and Germany maintain a relationship with NSO Group and have access to its spyware.
Timchenko, a resident of Latvia for nearly a decade, now posits that an EU member state may have targeted her in an effort to obtain information from her communications with other Russian journalists who recently departed Russia. Regardless of the origin, she characterizes the intrusion as an “expensive pleasure” for any state to have undertaken.
Timchenko and Kolpakov point to tensions arising late last year when Meduza became the first Latvia-based outlet to publicly support another independent Russian media group, TV Rain, which was expelled from Latvia due to accusations by a state broadcasting regulator that it posed a threat to Latvian national security.
While Meduza’s open letter of support for press freedom criticized TV Rain’s infractions, it lauded the exiled Russian outlet as one of the “few truly independent media outlets” with a substantial audience within Russia. Meduza commended TV Rain’s staunch anti-Kremlin stance and its opposition to the Ukrainian invasion.
The publication of this letter marked the first instance of Latvian journalists expressing support for Meduza. Consequently, it also drew criticism towards Timchenko’s organization. This criticism is what the journalists now perceive as the possible motivation for Latvian authorities or other entities to surveil Meduza.
Kolpakov suggests, “Now it is likely that the hack was operated by some European security service. We don’t know if it was Latvia or some other country, but we have more [presence] in Latvia.”
Notably, neither Latvia nor Germany, where the hack occurred, have initiated investigations into the breach, despite widespread reporting.
The Biden administration has taken a strong stance against NSO and other spyware companies, categorizing them as threats to U.S. national security. A U.S. State Department spokesperson condemned the harassment and extrajudicial surveillance of journalists, expressing solidarity with independent Russian journalists who expose the Kremlin’s actions against Ukraine.
Latvia, which has maintained a robust reputation for safeguarding press freedoms, denies any knowledge of electronic surveillance measures against Timchenko, asserting that it has provided a secure environment for independent Russian media and their staff.
The German Federal Police (BKA), an NSO customer since 2019, has refrained from disclosing information regarding the capabilities or tools used in covert operations.
These developments come in the wake of an extensive inquiry by a European Parliament committee into spyware abuses by European governments, including Hungary, Spain, Greece, and Poland.
Sophie in ‘t Veld, a Dutch Member of the European Parliament who spearheaded the investigation, expressed dismay at the utilization of “totalitarian tactics” within EU states. She noted that governments within the EU continue to employ Pegasus and similar spyware tools without adequate oversight or intervention by national governments or the European Commission.
In her words, “People have often said this whole spyware story compares to the European version of Watergate. It’s not. It’s more like The Lives of Others,” alluding to the pervasive surveillance depicted in the Oscar-winning German film set in East Germany during the 1980s.
In ‘t Veld emphasized that the issue extends beyond concerns of totalitarianism and emphasizes the need for transparency in the use of spyware by governments. She noted that the proportionality and legitimacy of such usage remain largely unknown.
NSO has initiated an investigation into the matter. The company maintains that it exclusively provides its potent hacking tools to government agencies for the purpose of investigating serious crimes.